الامتثال لـ GDPR لـ SaaS العالمي: مخطط فني
Executive Summary
The General Data Protection Regulation is not a legal checkbox to be delegated and forgotten—it is a systems architecture discipline that, when engineered with precision, becomes a durable competitive asset. For global SaaS organizations, treating GDPR as a technical specification is the only path to durable, defensible compliance.
The GDPR as an Engineering Problem, Not a Legal One
There is a persistent misconception that the GDPR is primarily a legal challenge. This framing produces surface-level legal theatre like cookie banners that provide negligible protection. In reality, the GDPR is a data systems architecture specification defining how personal data must be collected, stored, processed, and deleted. The individuals most responsible for compliance are data architects and backend engineers.
Foundational Concepts: What Global SaaS Teams Must Internalize
Personal data encompasses any information relating to an identified or identifiable natural person—including IP addresses, device IDs, and inferred behavioral data. Special category data carries even higher obligations. SaaS organizations frequently act as both Controllers and Processors simultaneously, and conflating these roles in internal architecture is a critical error.
Data Mapping and Processing Inventory: The Prerequisite Infrastructure
No compliance architecture can be correctly designed without a complete Record of Processing Activities (ROPA). This requires systematic data discovery—inventorying collection points, storage locations, processing operations, and geographic data flows. This must be maintained as a living infrastructure artifact, updated with every architectural modification.

Lawful Basis Architecture: Engineering Consent and Legitimate Interest
Every processing operation requires a lawful basis. Consent must be freely given, specific, and unambiguous—not bundled into terms of service. Legitimate Interest is not a convenient alternative; it requires a documented three-part test (Purpose, Necessity, and Balancing) to be valid.
Data Subject Rights: Building the Technical Fulfilment Layer
Fulfilling data subject rights (Access, Erasure, Portability, etc.) is not a manual support process—it is a technical capability. Erasure must propagate across backups, analytics platforms, and sub-processors. Portability requires structured, machine-readable export endpoints.
Privacy by Design and by Default: The Architectural Mandate
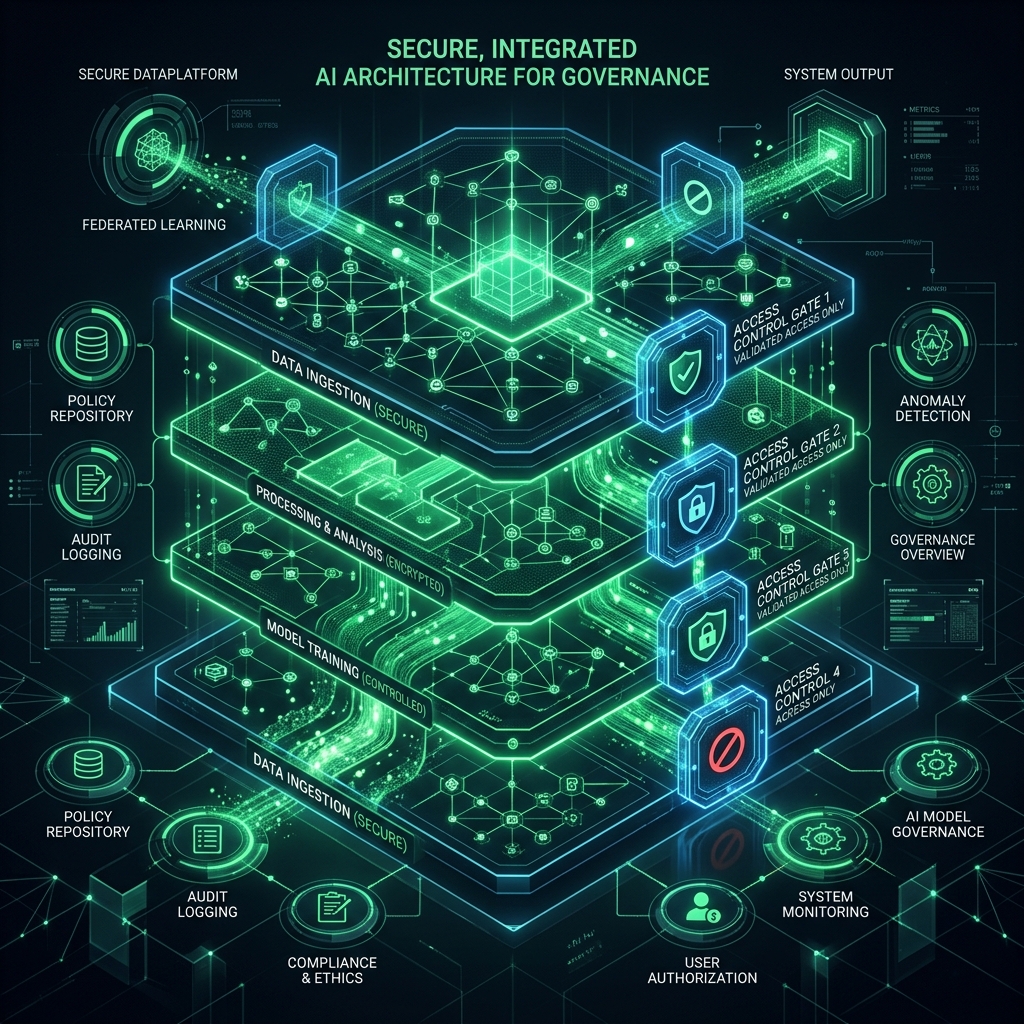
Article 25 enshrines Privacy by Design as a legal obligation. This requires threat modeling for privacy, pseudonymization as a default pattern, and encryption by design. Privacy by Default ensures that the most protective option is active without user intervention.
Security Architecture Under GDPR: Article 32 Unpacked
Article 32 requires technical and organizational measures appropriate to the risk. This baseline includes encryption at rest (AES-256) and in transit (TLS 1.3), rigorous Role-Based Access Control (RBAC), and network segmentation that isolates personal data environments.

Breach Detection and Notification Infrastructure
The 72-hour notification window for breaches is one of the most demanding operational requirements in the regulation. Meeting this window requires SIEM integration with real-time alerting on anomalous data access patterns and a predefined breach classification playbook.
Conclusion: Compliance as Precision Infrastructure
SaaS organizations that achieve durable, defensible compliance treat it as a systems engineering project. They build data maps as infrastructure and design rights fulfilment as a technical pipeline. Organizations that architect compliance with rigor do not merely avoid liability—they build a structural trust asset that serves as a competitive differentiator.